Public Security Test of the Covid Certificate: BFH assists with security
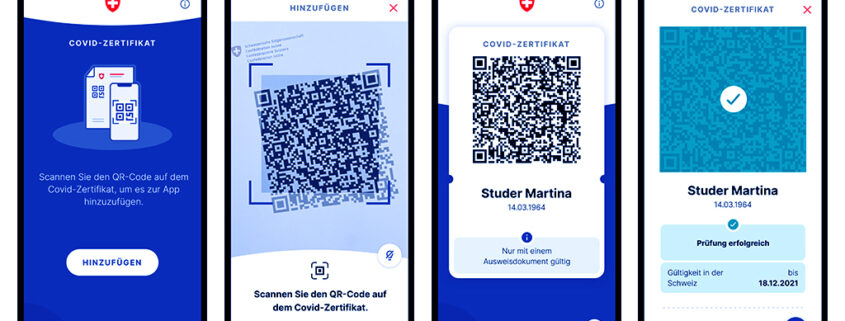
The first Covid certificates have been issued in the cantons since 7 June 2021. At the end of June, the system is to be introduced throughout Switzerland and will have a very high level of security. The IAM research group of the Institute for Data Applications and Security (IDAS) of the Bern University of Applied Sciences (BFH) is involved in the public security test.
A current version of the source code and a special test infrastructure are available for this public security test. The BFH research group, which focuses on electronic identities and privacy protection, sees it as one of its most important tasks to support such public projects with its entire expertise.
How does one proceed?
Testing is similar to looking for a needle in a haystack. Therefore, it is important to proceed systematically and document all results, whether positive or negative. One also tries to automate tests so that they can be easily repeated. By repeating on an updated version, one can then also prove that a gap or vulnerability has been closed.
- Definition of a test target: The attack vector on the system is defined. The following question is usually used for selection: What is the most worthwhile attack scenario?
- Analysis of the infrastructure: The architecture around the Covid certificates has been published ( https://github.com/admin-ch/CovidCertificate-Documents). Depending on the set goal and one’s own competencies, one chooses the components that promise the most relevant investigation results.
- Setting up a test environment: With the help of the publicly available code, an environment is set up with which many variants (more or less) can be quickly tested and documented automatically. The prerequisite is access to the Covid certificate test environment, for which one must apply for access (see: https://github.com/admin-ch/CovidCertificate-Apidoc#howto-become-a-system-integrator-using-the-api– ).
- Testing: One analyses the selected components and looks at the documentation. Then comes the creative part. You have to break away from the preconceived process or the documented functionality and try to do something different. To do this, you can, for example, change input data and try to omit or extend the parts or even fill them with random content.
First results
The BFH researchers initially focused on the management API in the backend that generates the QR codes and PDF documents. The errors found so far are not serious and do not pose a security risk. Nevertheless, finding and then fixing small security gaps helps to secure and stabilise the overall system. In the coming weeks, researchers at IDAS will continue their efforts to further increase the trust and reliability of Covid certificates and issuing systems. This will contribute to the acceptance of the Covid certificate, the vaccination and thus the fight against the pandemic.
The first notification found
The notification submitted and accepted by the BIT (see: https://www.ncsc.admin.ch/ncsc/de/home/dokumentation/covid-certificate-pst/current_findings.html ) is not critical with regard to the overall system, as the affected management API in the backend is very well protected with the help of personal TLS certificates and a one-time password (so-called OTP) valid for 12 hours, which can only be generated by authorised users. Since this interface is to be used in the future by medical practice systems or pharmacist software, it is important to systematically check all data sent and reject errors or invalid information. Only in this way can a high quality of the certificates be achieved.
 Create PDF
Create PDF
 Contributions as RSS
Contributions as RSS Comments as RSS
Comments as RSS
Leave a Reply
Want to join the discussion?Feel free to contribute!